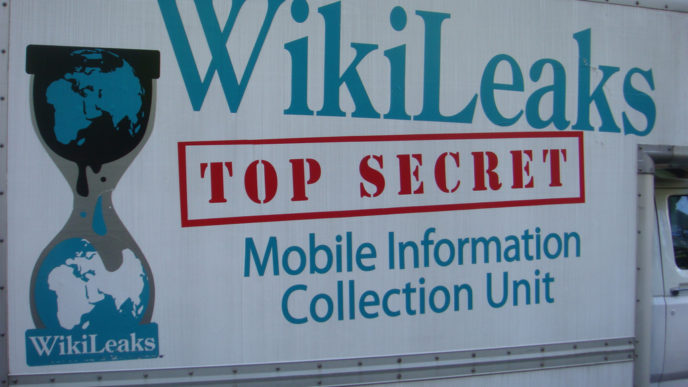
WikiLeaks Publishes ‘Biggest Ever Leak of Secret CIA Documents’, Reignites Questions Whether CIA Assassinated Michael Hastings
By Ewen MacAskill. The US intelligence agencies are facing fresh embarrassment after WikiLeaks published what it described as the biggest ever leak of confidential documents from the CIA detailing the tools it uses to break into phones, communication apps and other electronic devices.
The thousands of leaked documents focus mainly on techniques for hacking and reveal how the CIA cooperated with British intelligence to engineer a way to compromise smart televisions and turn them into improvised surveillance devices.
The leak, named “Vault 7” by WikiLeaks, will once again raise questions about the inability of US spy agencies to protect secret documents in the digital age. It follows disclosures about Afghanistan and Iraq by army intelligence analyst Chelsea Manning in 2010 and about the National Security Agency and Britain’s GCHQ by Edward Snowden in 2013.
The new documents appear to be from the CIA’s 200-strong Center for Cyber Intelligence and show in detail how the agency’s digital specialists engage in hacking. Monday’s leak of about 9,000 secret files, which WikiLeaks said was only the first tranche of documents it had obtained, were all relatively recent, running from 2013 to 2016. (Read more from “WikiLeaks Publishes ‘Biggest Ever Leak of Secret CIA Documents'” HERE)
___________________________________________
WikiLeaks Publishes Information Reigniting Questions Whether CIA Was Involved in US Journalist Hastings’ Death
WikiLeaks’ release on Tuesday of a massive trove of secret CIA documents has reignited conspiracy theories which have swirled since 2013, with revelations the spy agency was attempting to remotely hack vehicles.
“As of October 2014 the CIA was also looking at infecting the vehicle control systems used by modern cars and trucks,” WikiLeaks writes. “The purpose of such control is not specified, but it would permit the CIA to engage in nearly undetectable assassinations.”
Hastings, an acclaimed war correspondent and vocal critic of government mass surveillance, died in the early hours of Tuesday, June 18, 2013, when his Mercedes C250 Coupe apparently lost control and burst into flames before slamming into a palm tree. . .
[F]ormer US National Coordinator for Security, Infrastructure Protection, and Counter-terrorism Richard Clarke told The Huffington Post the crash was “consistent with a car cyber attack”. . .
WikiLeaks itself appeared to suggest Hastings’ death was the result of foul play. Hours after crash, WikiLeaks tweeted: “Michael Hastings contacted WikiLeaks lawyer Jennifer Robinson just a few hours before he died, saying that the FBI was investigating him.” (Read more from Wikileaks Publishes Information Linking CIA to Hastings’ Death HERE)
Editor’s note: To learn more about the troubling facts surrounding Hastings death, please click HERE.
___________________________________________
FBI Prepares for New Hunt for WikiLeaks’ Source
By Devlin Barrett. The FBI has begun preparing for a major mole hunt to determine how anti-secrecy group WikiLeaks got an alleged arsenal of hacking tools the CIA has used to spy on espionage targets, according to people familiar with the matter.
The leak rattled government and technology industry officials, who spent Tuesday scrambling to determine the accuracy and scope of the thousands of documents released by the group. They were also trying to assess the damage the revelations may cause, and what damage may come from future releases promised by WikiLeaks, these people said . . .
In the wake of revelations from Army private Chelsea Manning and former National Security Agency contractor Edward Snowden, officials sought to tighten security procedures, and federal agents came under greater pressure to find and prevent secrets from spilling out of the government. (Read more from “FBI Prepares for New Hunt for WikiLeaks’ Source” HERE)
___________________________________________
WikiLeaks Says It Releases Files on CIA Cyber Spying Tools
By Reuters. Anti-secrecy group WikiLeaks on Tuesday published what it said were thousands of pages of internal CIA discussions about hacking techniques used over several years, renewing concerns about the security of consumer electronics and embarrassing yet another U.S. intelligence agency.
The discussion transcripts showed that CIA hackers could get into Apple Inc iPhones, Google Inc Android devices and other gadgets in order to capture text and voice messages before they were encrypted with sophisticated software.
Cyber security experts disagreed about the extent of the fallout from the data dump, but said a lot would depend on whether WikiLeaks followed through on a threat to publish the actual hacking tools that could do damage.
Reuters could not immediately verify the contents of the published documents, but several contractors and private cyber security experts said the materials, dated between 2013 and 2016, appeared to be legitimate. (Read more from “WikiLeaks Says It Releases Files on CIA Cyber Spying Tools” HERE)
Follow Joe Miller on Twitter HERE and Facebook HERE.